Easy Steps to Finding the Private SBOMs You Need
A secret SBOM has no value. In fact, it has no meaning; an SBOM only exists to share critical information with trusted parties so that they can make confident decisions about the software they purchase and run. But that does not mean that all SBOMs should be shared publicly. In reality, the majority of SBOMs will need careful and confidential sharing only with those people that need to know and have permission to view them. But this sets up a further conundrum; how do you know that a private SBOM exists, where do you go to find it, and how can you prove you have permission to see it?
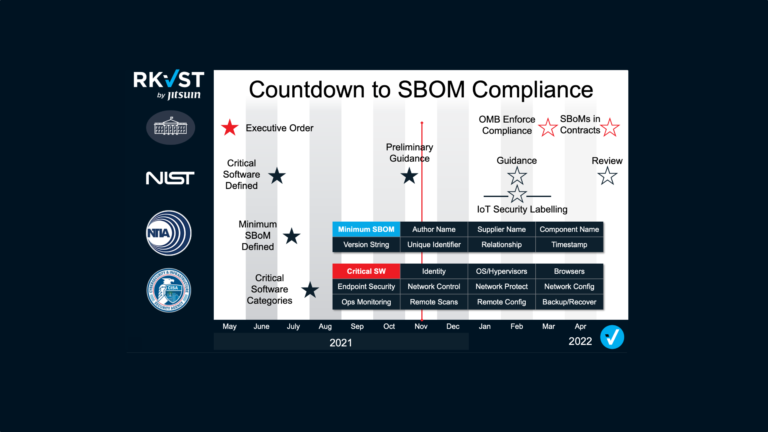
Needles in haystacks
Since President Biden’s Executive Order last spring, the industry has been racing to define, standardise and now produce SBOMs to describe the hundreds of thousands of software products sold to and used by federal government and beyond. So far, little thought has been given to the management of SBOMs in practice. Finding the right SBOMs for all the software an organisation relies upon can already feel like hunting for needles in haystacks. Different publishers store, share and publicise their SBOMs in different ways and in different places. No one wants, or can afford, to create ‘SBOM departments’ to manage this work. The RKVST SBOM Hub was established to simplify this task as a single destination for people to find and fetch the SBOMs they need.
But what if software is proprietary or licensed commercially, as most software is? Neither publisher nor subscriber will want to reveal its contents in a publicly shared SBOM. As a consumer how do you know if the SBOM exists, and where to find it? As a publisher, how can you show compliance (and demonstrate industry best practice) without revealing commercial secrets? Now the issue becomes more like looking in haystacks for a needle you’re not sure even exists!
Enter the RefBOM
With RKVST we are pioneering the use of RefBOMs to solve this issue. Quite simply, a RefBOM is a signpost to a private SBOM. It demonstrates the existence and provides a route to accessing an SBOM which is only to be shared with specific parties with right credentials and permissions. Developers and software publishers can easily create a RefBOM that testifies to the existence of an SBOM for a specific piece of software or code and share it in the RKVST SBOM Hub. Anyone looking for an SBOM for that specific software can search and find the RefBOM and so be assured that an SBOM for the software exists.
However, clicking on the RefBOM link will take them to page informing them that they can only view the SBOM if they have permission. Using a unique and secure RKVST ID they can request permission to see the full SBOM. RKVST gives publishers a private repository where they can decide exactly who sees which SBOMs. If the request to view comes from someone with permission to view the SBOM then access can be granted. To see how simple this is watch how Device Authority has solved the challenge of SBOM sharing here:
Multiple parties, multiple roles
RKVST is designed for the real world. Developers may create SBOMs for their code initially, but many others, from governance risk and compliance teams to commercial and customer management roles will need to interact with them. Working from the principle of ‘verify – then trust’ RKVST enables organisations to impose their own governance rules on exactly how they want and need their SBOMs to be shared. Exactly who can grant permission to whom will be up to individual businesses to decide, but RKVST keeps an immutable record of who did what when to any asset providing assurance that only those that need to know are able to view the SBOMs they need. Using secure APIs and cloud architectures, all of this can be automated. As SBOMs become increasingly mainstream many are realising that managing access to thousands of SBOMs all with different levels of permission could rapidly become a bureaucratic nightmare. Seeking to manage the exchange of this information using manual and human-centric processes is neither scalable nor productive. Automating the storage, discovery, sharing, governance and security of SBOMs is the only way forward.
To find out more about how RKVST delivers all of this visit www.RKVST.com or explore the RKVST SBOM Hub