Solutions
See how RKVST makes it easier for businesses to share data in these real-world examples

ESG accountability for the aviation carbon offset market
Underpin sustainability claims for climate-neutral aviation
Green aerospace company SATAVIA has the mission of cutting up to 60% of aviation’s climate impact via contrail prevention. Immutable storage of flight-by-flight data, with clear oversight of provenance and governance – a central requirement of climate benefit accounting.
SATAVIA deployed RKVST to provide a single immutable source of truth, storing key information relating to each modified flight and the climate benefit achieved from each flight modifications.
Read the SATAVIA case study
Benefits
- A single source of truth
Data provenance and integrity, providing a single source of truth for key information relating to each flight modified for contrail prevention and the associated climate benefits. - Time to market
SATAVIA was able to develop a viable solution within weeks rather than months, without the need to write custom code or interfaces, neither did it need to recruit and train blockchain specialists. - Auditable chain of custody
An auditable chain of custody, enables reliable sustainability reporting that meets the fundamental requirements of climate benefit accounting and the generation of carbon credits.

Accelerating nuclear waste material handling
Bridging the trust gap in nuclear waste handling
Together with Digital Catapult, the UK authority on advanced digital technologies, Sellafield was looking to evaluate novel solutions that could create a trusted and secure record for tracking hazardous waste and materials throughout the nuclear industry.
Sellafield chose RKVST for its ability to accurately represent physical handling lifecycles in a high integrity record that provides reliable access to all stakeholders to do their job with minimal disruption to existing systems and processes. Through RKVST track-and-trace of waste assets, Sellafield and Digital Catapult forecast significant cost savings and handling speed improvements with vastly increased reliability and data accuracy.
Read the Sellafield case study
Benefits
- Know your things
Complete traceability of provenance, operations, and maintenance for the life of the asset wherever it is - Minimize transcription errors
Consistent physical-to-digital mapping means all stakeholders know they’re dealing with the right items, and a single source of truth eliminates the use of stale, incorrect, or mistyped data - Integrate with existing systems
Get the benefits of Blockchain without major disruption to software systems and processes

Zero Trust IoT Devices
Advanced Zero Trust authorization
The modern approach to cybersecurity is Zero Trust: don’t place all faith into a single component, rather continuously verify trustworthiness for every authorization.
Typical IoT solutions & devices rely on standard approaches to authentication, such as PKI certificates, to verify device identity and trust devices. However, many other systemic issues such as firmware bugs, cloning, or missed maintenance SLAs can mean the device and its data are not trustworthy and pose a threat.
Device Authority chose RKVST for its ability to gather and distribute the trustworthy supply-chain-wide security and maintenance information that is essential to making reliable real-time zero trust authorization decisions where the compromise of legitimate devices poses a threat.
Benefits
- Controlled SBOM distribution
Complete traceability of device software provenance, but only for those who need to know. - Advanced composition analysis
SBOM is just the start: knowledge of where the software is deployed, how it has been handled, and whether it is up-to-date fuels higher quality decisions - Reduce IoT risk
Automated Zero Trust decisions underpinned by checks on SBOMs and other lifecycle events reduce the risk of compromised devices entering your network.

Trust your digital operations
Powering Product-as-a-Service digital transformation
Siemens Drive Technology issued a Global Challenge to find solutions that would enable the confident launch of a “motion-as-a service” digitally transformed business model where customers pay for the motion delivered rather than buying capital equipment.
Siemens chose RKVST for its capabilities in assured collaborative operations. The platform’s distributed architecture, data integrity features, and flexible user authentication enables all stakeholders to share the right data at the right time. This aligns incentives for reliability and service delivery for customers and better operational data and profitability for Product-as-a-Service providers.
Benefits
- Know your things
Complete traceability of provenance, operations, and maintenance for the life of the asset — even after exchange or transfer - Find and fix faults fast
Near real-time insight into process breaches across the supply chain: less time searching, more time doing - Boost your digital transformation
Automate digital business processes with confidence in your data and trust throughout the value chain

Turn chain of custody into chain of responsibility
Bringing trust to Digital Twins for the construction industry
Lendlease needed deep and dependable supply chain traceability of construction materials in order to automate and digitize the building design and approval process with trusted digital twins replacing paper and signatures.
Lendlease chose RKVST due to its distributed architecture, data integrity features, and simple code integration which enables confidence that the physical supply chain matches the digital model and unlocks the power of Digital Twins for designing the built environment.
Benefits
- Automate CM processes
Proof-of-compliance at every stage gives confidence in fast changes and rapid iteration while ensuring accountability for externals - Prove faulty parts & suppliers quickly
With a detailed trusted and traceable history, problems can be quickly resolved and dangerous flaws remediated before things go wrong - Keep familiar tools and processes
API-first approach enables integration of RKVST behind existing procurement and supply chain tooling. Minimal disruption for customers and suppliers

Accountability for connected buildings
“Watching the watchmen” for building access management
Wavestone needed to deliver strong regulatory oversight of overridable electronic door locks. The evidence trail required the highest levels of integrity while preserving personal privacy for building residents. Once solved, this offered the ability to expand usage of convenient access while proving the highest level of trustworthiness to citizens.
Wavestone chose RKVST as the trustworthy transparency platform their customer needed. The platform’s secure, privacy-first data sharing features gave them the strong evidence trail that all stakeholders needed, while its cybersecurity supply chain traceability features massively cut the cost and time to prove compliance, integrity, and provenance of that data.
Benefits
- Know your things
Complete traceability of provenance, operations, and maintenance for the life of the asset and the data underpinning digital transformation - Justify authority and increase customer trust
Adopt a transparency-first approach to super-user capabilities opening operational opportunities through strong accountability - Deter abuse
Ensure all use is permanently recorded and abuses can be found early, boosting confidence in remote and shared digital operations
Discover RKVST for yourself
Achieve provenance, governance, and immutability for your shared data with none of the costs, distractions and diversions.
Recent Posts
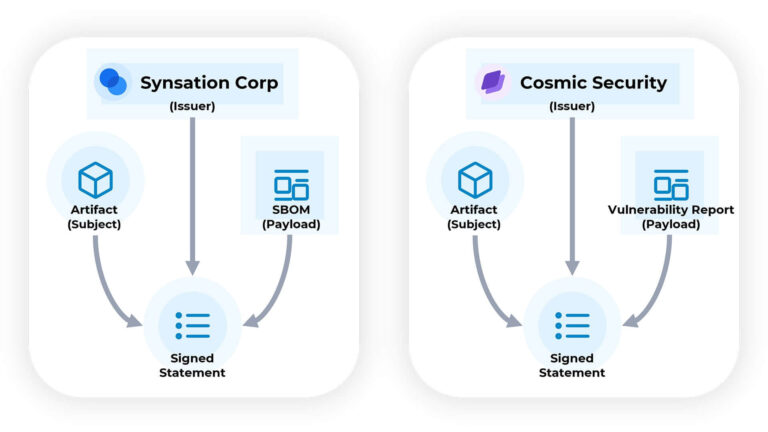
Creating DataTrails for Supply Chain Artifacts
Staying informed about your software means consuming information from various sources and knowing when and where to apply that information.
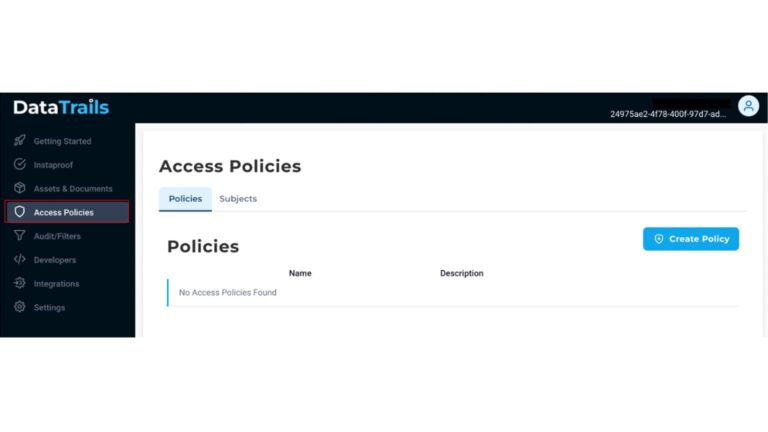
Customize your Access Policies with DataTrails
Signing up with DataTrails comes with the ability to share your audit trails with your business partners, other applications, and your internal team. Access policies control users, apps & organizations’ read & write privileges to provenance…
What is Data Provenance?
Everything you need to know about Data Provenance Data provenance is a technology field that aims to help businesses increase trust through transparency of data, specifically by tracking the origin, change, and history of data and…