Supply Chain Integrity, Transparency, and Trust
SCITT in the information security context stands for “Supply Chain Integrity, Transparency, and Trust”. It’s a relatively young discipline and the dust is still settling over its scope and definition but the core is very simple: risk vests in the operator of equipment, but it originates at every point in the supply chain. If we are to take control of – and responsibility for – our own cyber-physical risk then it is essential to know what we’re dealing with: How was this machine made? Who has touched it along the way? What sensitive components are inside it? And crucially, how do I prove to my own and my auditor’s satisfaction that it is safe and secure to operate?
The answers to all of these questions are much easier to find if supply chain partners collaborate and share data about shared assets and processes in a spirit of transparency, accountability, and trust.
Why now?
1. Solarwinds, Kaseya, …
There have been a number of high-profile security breaches in recent years, along with the prolific rise in ransomware, which have served to raise the visibility of supply chain attacks as a top cyber issue. Of course, attacks have been happening for years without people taking them terribly seriously, so what’s new? Well, governments have now started pushing the priority more seriously than ever before, and at the same time, companies are beginning to drown under the weight of managing threat exposure.
According to the UK National Cyber Security Centre:
The compromise of the software company SolarWinds and the exploitation of Microsoft Exchange Servers highlighted the threat from supply chain attacks. These sophisticated attacks, which saw actors target less-secure elements – such as managed service providers or commercial software platforms – in the supply chain of economic, government and national security institutions were two of the most serious cyber intrusions ever observed by the NCSC.
https://www.ncsc.gov.uk/collection/ncsc-annual-review-2021/the-threat
2. Whitehouse Executive Order
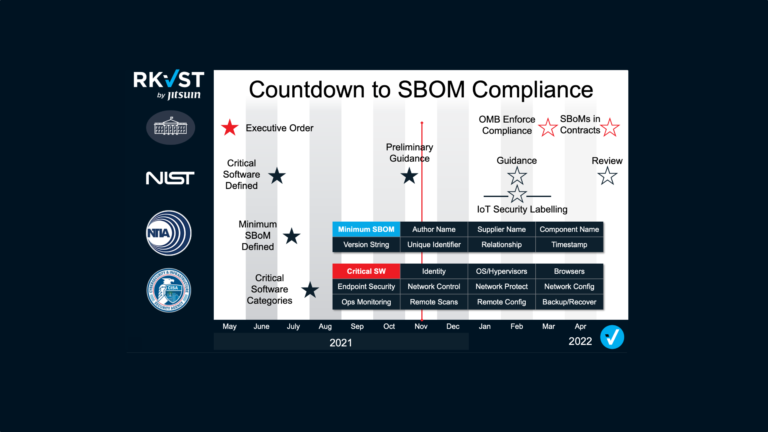
Just over a year ago the Whitehouse published Executive Order 14028, which we commented on here. In common with moves from other governments in recent years, the order highlights the need to transition to a Zero Trust mindset with supply chain transparency and trust a major pillar of that.
The first flurry of activity around 14028 was concerned specifically with Software Bills of Materials, or “SBOMs” (check our other blogs for extensive information about this, or just head straight on over to datatrails.ai/share-sboms/ to get started) but it quickly evolved to recognize that generating SBOMs is not enough: you also need secure ways of sharing them with the right stakeholders, of analyzing them with the right risk information, and ultimately using them to make strong, confident zero trust decisions based on data from your now very digital supply chain.
3. National Cybersecurity Centre of Excellence
Alongside its great efforts to promote and improve the implementation of Zero Trust Architectures, NCCoE is running a project to improve supply chain assurance which focuses on many similar themes. The project aims are stated as:
Technologies today rely on complex, globally distributed and interconnected supply chain ecosystems to provide highly refined, cost effective, and reusable solutions. Organizations currently lack the ability to readily distinguish between trustworthy and untrustworthy products. Having this ability is a critical foundation of cybersecurity supply chain risk management (C-SCRM).
https://www.nccoe.nist.gov/supply-chain-assurance
NOTE that the NCCoE best practice guides are open for comment until July 25th, 2022, so at time of writing you still have 2 weeks to influence the work. Please do get involved if you have something to contribute!
4. IETF SCITT non-Working Group
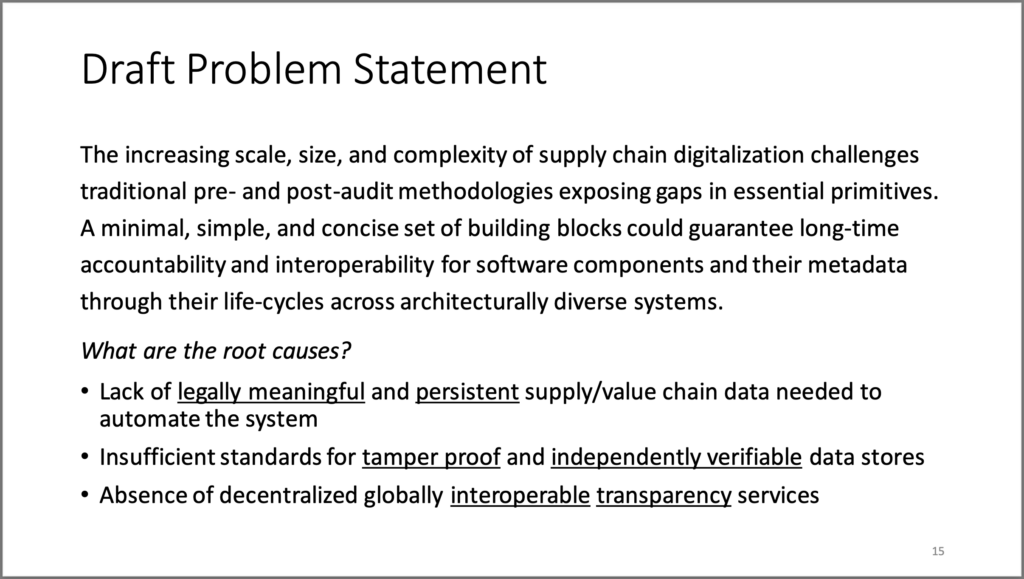
In March of this year, a new SCITT non-WG group was created under the IETF to tackle this problem:
In the exchange of artifacts across end-to-end supply chains, it is often the case that receiving entities require evidence to verify the suitability of artifacts for an intended use. Key questions are how the authenticity of entities, evidence, policy and artifacts can be assured and how the evidence provided by entities can be guaranteed to be authorized, transparent, immutable and auditable.
“About SCITT”: https://www.ietf.org/mailman/listinfo/Scitt
Following very positive activity in the community a refined version of this problem statement was presented at a well-attended Birds of a Feather session (slides) which dived deeper into the challenges and opportunities of implementing and using supply chain trust in the real world. This problem statement clearly lays out the need for a new approach to trust in increasingly digital or digitized supply chains:
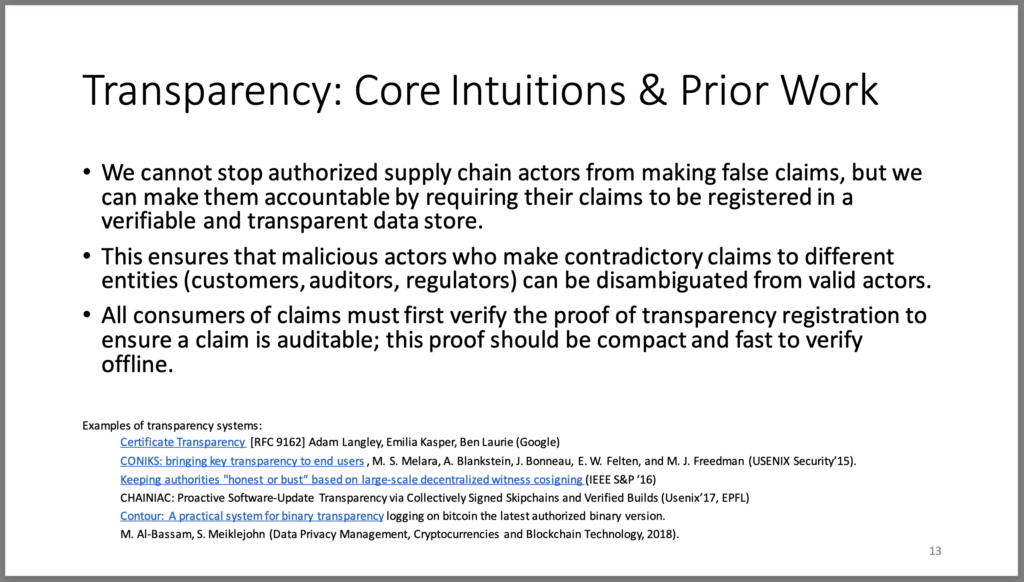
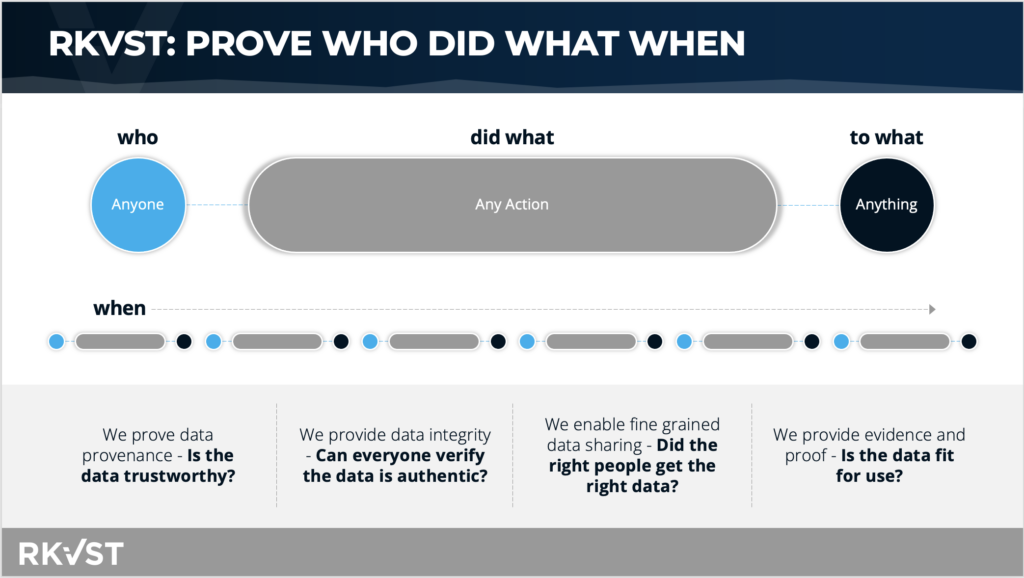
Alignment with DataTrails
All four of these strong industry-proof points have strong common themes, and here at DataTrailswhen we talk about the Trust Gap, those themes are exactly what we’re talking about. Rather than write more words, these 2 slides from our standard pitch deck illustrate how well-aligned we are with the NCCoE and IETF SCITT communities.

In fact, as you can see from this video showing an implementation of a decentralized service for ensuring trust in industrial cybersecurity supply chains (originally created in 2019, sorry for the rather rustic production values), DataTrails (then still branded ‘Jitsuin’) has been focused on this problem space from the very beginning, and we couldn’t be more excited to see the space hotting up and starting to get the recognition it deserves!
Growing awareness
Unfortunately, while there is increasing activity in the expert community, we still have a way to reach the market. Searching for SEO data on “Supply chain integrity transparency and trust”, or even just “Supply chain integrity” yields no data at all. “SCITT” on its own has a lot of data but none of it is associated with digital technology or supply chains: it’s mostly education-focused.
It also has dismal hashtag statistics (and this time it looks like they’re all education-related):
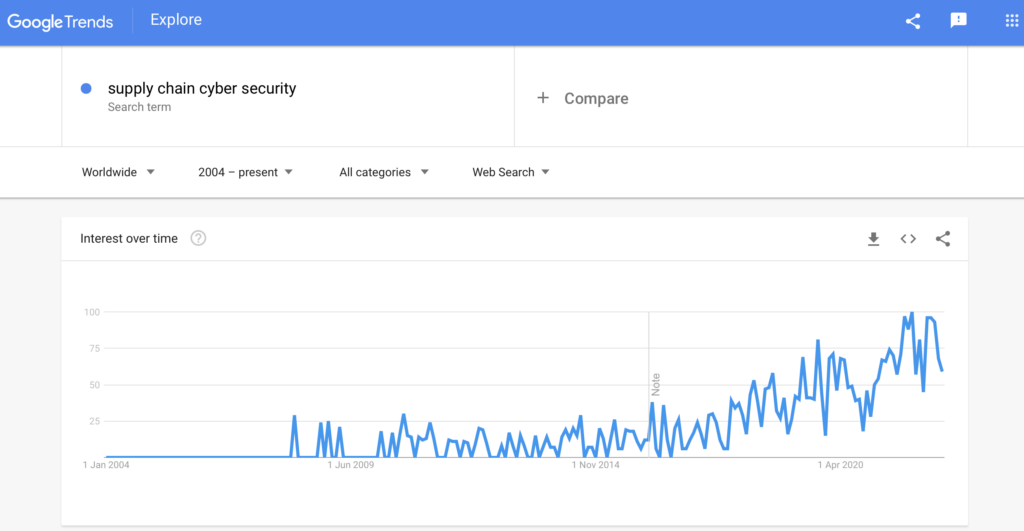
All is not lost, however. People are searching for solutions to these problems…they’re just not necessarily looking in the right place or for the right solution. Interest in “Supply chain cyber security” has been growing steadily over the past 10 years:
So what’s the difference? As we have written and presented before in various places there needs to be a shift in mindset from bulletproof security and silver bullets toward a spirit of zero trust, shared intelligence, and resilience in the face of emergent threats. Things are only secure until they’re not, and trust is contextual so it’s not enough to do an audit or security report once and then rely on that for months later: you need to continuously verify security and trust posture in near real-time, assume breach, and then quickly deal with problems when, not if, they arise.
This isn’t just peddling scary stories about cyber terrorists or APTs: many seemingly innocent or accidental things can also affect security and trustworthiness between organizations including different risk exposure, different personnel capabilities, different training regimes, or different practical operating constraints. And of course, everyone has different commercial motivations: not everyone in a supply chain is unerringly good…
To cope with all of this, we need to move from the impossible task of trying to make cheating and threats impossible, to the more tractable one of detecting and mitigating threats as they arise. An extreme but essential aspect of this to understand is that SCITT does not prevent attacks or bad actors but it does hold them accountable through the principle of transparency. If someone cheats (or simply screws up) too often then they will be ostracised by the group. If someone refuses to act transparently they will struggle to gain business. And in the end, the result of this is market forces that incentivize everyone to hold themselves accountable and accept responsibility for their own informed risk.
Once this principle (and its close cousin ‘attestation’) is internalized, the security benefits of SCITT suddenly become clear.
SCITT is a Team Sport
We’re going to be piling into SCITT and supporting the development of standards in this area, and we think you should too! This area can only be served by a flourishing ecosystem of providers: interoperability and information exchange are key. We have a growing set of partners providing solutions in the digital supply chain space, and if you want to join the program we’re very happy to hear from you.